
Business Education
Webinars, blogs, and more
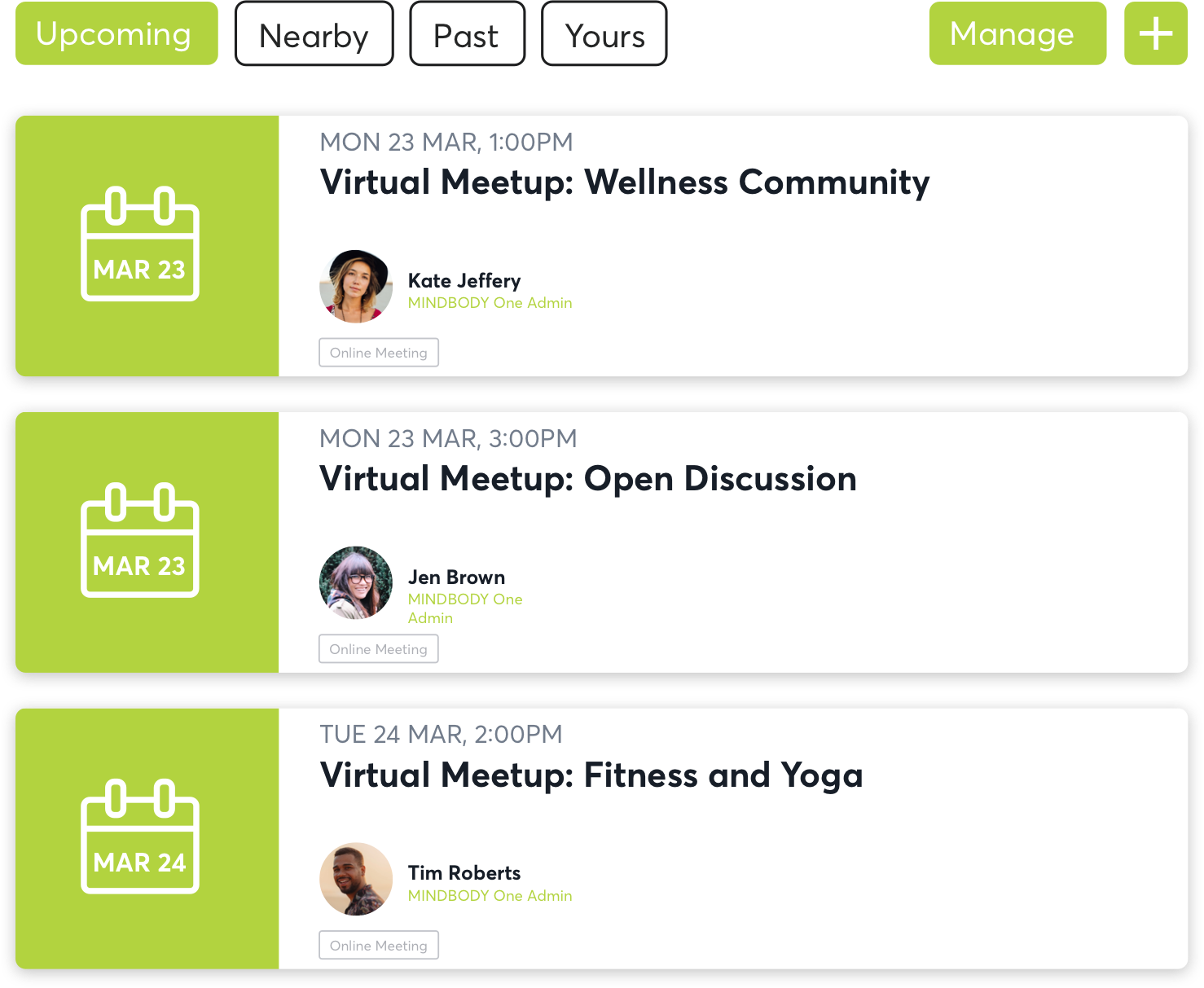
Mindbody One is here for you
Connection is more important now than ever. The Mindbody One community wants to help you find other business owners experiencing the same challenges that you are. Ask questions, share feelings, and get advice from people who truly understand.

New resources, straight to your inbox
Get updates on the latest industry trends, tips, and news.









